January 2015 – The Month in Email
It’s February already! January went fast, right? At WttW, we are gearing up for MAAWG SF later this month — will we see you there?
We started the year with a set of predictions about email. Mostly we think email will continue to be great at some things and not-so-great at other things, and we’ll keep fighting the good fight to make it better.
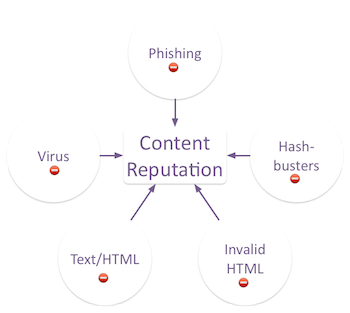
As always, I’m interested in filters and how spammers continue to work around them to reach the inbox. I also wrote about how the language of an email impacts delivery, and wrote an expanded response to a comment suggesting email filters should be illegal. You can guess where I stand on that (and if you can’t, perhaps you might read more about how email is an inherently malicious traffic stream…)
I also took a moment to point out a trend I’m really enjoying, which is the rise of content marketing (a.k.a. giving customers useful and interesting information they can’t find elsewhere). As I said in the post, I’ll be curious to see how ROI plays out with this strategy.
We also talked about some of the less exciting content we see in email, notably the infamous Murkowski Statement, by which a spammer declares “Nope! Nothing to see over here!”
Steve also pointed out some content shenanigans in the form of hidden preview text, with some additional clarification from the original marketer in the comments.
In industry news, the big story was that Microsoft has partially implemented DMARC for Office365, and was the first to make a public statement about the specific ways they’ve chosen to implement. In my post, I did a walkthrough of a message to illustrate a bit about how this works, which might be useful if you’re trying to wrap your head around DMARC implementations.
We also talked about consolidation in the ESP space, and got a number of comments from readers about who they think might be next. Shortly thereafter, Listcast was acquired by MailerMailer.
Josh noted a few major shutdowns: Yahoo China email services and the AHBL list. The latter explores the challenges inherent in decommissioning a blacklist, and there’s a good discussion in the comments, so you might check it out if you missed that earlier this month.
Josh also pointed to the Salesforce State of Marketing report, which is always a useful set of metrics about how marketers are using email and other channels. It’s definitely worth a read.