Equifax compromise and their insecure response
Today it was announced that someone infiltrated Equifax earlier this year and stole 143,000,000 identities. These identities include names, birthdates, and addresses, at a minimum. Details are available at your favorite news site.
What I want to talk about is the website they’ve put up to address the issue. This website is Yet Another Example of how the financial services industry trains users to be phishing victims.
Equifax set up a website for people concerned about the possibility of identity theft after this major data leak. The URL, as distributed by the press and linked to from Equifax’s own website is https://www.equifaxsecurity2017.com.
When I was first sent to the site, I thought it was a phishing site because there is absolutely no way to confirm this site is owned and managed by Equifax. Zero. In fact, there’s a lot of evidence that the site isn’t owned by Equifax. And most of the rest of the evidence relies on trusting that the hackers still don’t have some level of access to Equifax systems.
Visiting the Website
The site does have SSL, but the certificate is issued to “ssl511860.cloudflaressl.com”. Cloudlfare has a somewhat sketchy history and I would not put it past them to host and protect a phishing site. So the SSL certificate doesn’t give me any faith this is Equifax.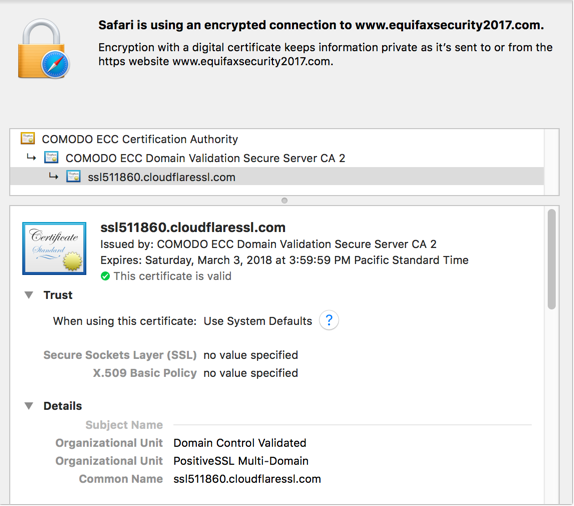
There’s a link back to Equifax’s pages, but that’s SOP for phishing, so no help there. Yes, I can get to the website from Equifax’s home page, but this URL is being given out in various press articles.
When we check the whois. The registrar is MarkMonitor but the registrant is some random company called DNStinations.
Registrant Name: Domain Administrator
Registrant Organization: DNStination Inc.
Registrant Street: 3450 Sacramento Street, Suite 405
Registrant City: San Francisco
Registrant State/Province: CA
Registrant Postal Code: 94118
Registrant Country: US
Registrant Phone: +1.4155319335
Registrant Phone Ext:
Registrant Fax: +1.4155319336
Registrant Fax Ext:
Registrant Email: admin@dnstinations.com
Registry Admin ID:
When I visit http://dnstinations.com/ I get an error message: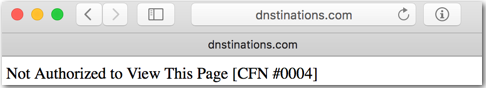 The domain owner has no website. That doesn’t reassure me.
The domain owner has no website. That doesn’t reassure me.
Now, when I drop the physical address into Google I get an address that’s listed as a Proxy Partner on the MarkMonitor website. At this point, I start to wonder if my faith in MarkMonitor is misplaced.
Of the things we can check on the website, the best assurance we have here is that MarkMonitor is a service that big companies use to protect their domains. Not that reassuring overall, but we’ll go with it.
ID Protection Services
We’ll assume the press has done some level of fact checking and this website is valid. We click on the link that says “enroll in ID protection” which takes us to a different website: https://trustedidpremier.com. The first thing it asks me for is my name and the last 6 digits of my social security number.
What evidence do I have that this website is valid? It has a SSL cert issued by Amazon. It’s hosted on EC2. The whois data is all behind privacy protection. The bare domain serves up an error message.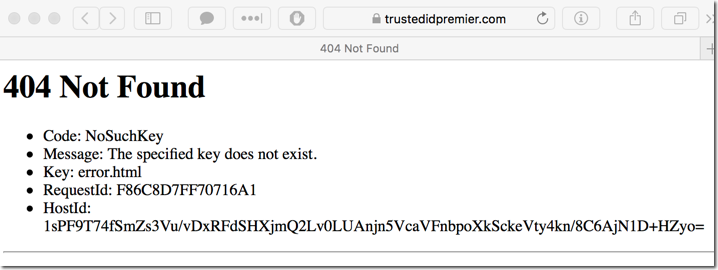
This is the website that they want me to trust to protect my identity?
It will work
The thing that really gets me is that most people are going to drop their information into this website. They’re going to go through whatever process is going on.
This is training for people to be phished. I’ve actually seen better phishing websites than this one. In fact, I’m more inclined to believe this is legitimate because phishing sites are done better!
Now, I’ve long believed that all my information is compromised and is out there for sale. I know some of it is. Two universities that had my info have lost it. I’ve had my credit card company send me new cards “for security purposes”. I shopped at Home Depot during their compromise. None of that is any of my fault, which is why I’m careful but not obsessively careful with personal info. I can’t control if it stays private. That’s clear.
But acknowledging that I can’t control my personal info doesn’t mean I am going to go around and drop my name and most digits of my SS number into some website as horribly set up as this one.
Equifax dropped the ball here, not just by their lax security but also by their insecure response to the compromise. (And that’s before we get to the fact that 3 senior Equifax executives sold 1.8 million dollars worth of stock after they found the compromise but before they announced it.) This isn’t unique to Equifax, Target dropped the ball, too, when they were compromised.
I was on a call today discussing DMARC. It’s great that email folks are stepping up to make email more trustworthy. But when a company pulls such a boneheaded move, in response to a major leak of data, I know that DMARC and email isn’t enough. We need to work towards a safer internet and that means companies have to step up and stop being stupid about cybersecurity.

