Social media connections are not opt-ins
- laura
- January 25, 2018
- Best practices
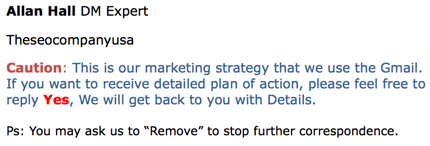
It seems silly to have to say this, but connecting on social media is not permission to add an address to your newsletter or mailing list or prospecting list or spam list. Back in 2016, I wrote:
[Scraping addresses from LinkedIn] is really rude. Just because someone accepted your contact request on LinkedIn, doesn’t mean they want to be added to any mailing lists you may have. Let’s be honest, some people have hundreds or thousands of LinkedIn contacts. They’re not going to want to get mail from all of them.
This behavior risks your ESP account. I know of ESPs who have disconnected customers for importing all their LinkedIn contacts. Harvesting Addresses from LinkedIn

In that blog post I wrote a number of suggestions for how to screen LinkedIn connections before sending them mail.
- Not everyone will necessarily be happy to receive this mail from you. Consider how closely you are connected with the person. Ask yourself: Would this person appreciate a commercial email from me or my company? If you don’t know the person well enough, then it’s likely that the answer will be no. Put a little time and energy into making sure that your message is going to be wanted. If that means dropping people you’re not sure about off your contact list, then do it.
- Consider sending out personal mails, not importing the email addresses into your CRM system or sending them out through your ESP. Don’t make the message look like a mass mailing. This is a social network, make your contact actually social.
- Think about what YOU are bringing to the relationship with the recipient. Are you actually offering them any value? With the Christmas card I received the message was “Our company is wonderful! We love ourselves. And we think we’re so great we’re going to send out this card telling you how we’re not sending out Christmas cards this year!” In Al’s case the message was adding him to a mailing list. In both cases, neither of us cared. There was nothing in it for us.
- If you want to announce a product and or service use the tools provided by the social networking service. LinkedIn has InMail, which allows recipients to set their contact preferences and mail through their system.
- If recipients object to your email, arguing with them is never helpful. You’re not going to convince them the mail is wanted, you’re just going to convince them that you’re an unrepentant spammer. Apologize, learn from it, move on.
Those are all still reasonable suggestions, ones that I’d offer to anyone who asked. But all those suggestions do is minimize the chance that the sender will get into trouble for sending spam. The fact is harvesting addresses and sending mail to them is spamming. Even if it’s B2B mail it’s still spam. Because it’s spam, even if you do everything I recommend you risk having some of those recipients object to the mail. Folks who object may complain to your ESP, they may disconnect from you on LinkedIn, they may block all future mail from your company, they may even convince their company to never do business with you. All of these are actual consequences I’ve seen happen.
When the sender is using a reputable ESP, the risks are even bigger. I also know of multiple cases where complaints resulted in the ESP disconnecting the customer for AUP violations. This is not something you want to happen.
B2B spam is still spam, and it’s not OK. Don’t be a spammer. Social media is called social for a reason.