There’s going to be a lot of hype today about something the security researchers who found it are calling “EFAIL”. Interviews, commemorative T-Shirts, press tours, hype.
The technical details are interesting, but the un-hyped end-user advice would probably be “If you’re using a mail client that’s got bugs in it’s MIME handling, and you’ve configured it to load remote content automatically, and you’re using a less secure encryption tool or protocol, and you’ve configured it to decrypt things automatically, and security of your email is so important to you that you’re defending against skilled attackers who have already acquired the encrypted emails you’re concerned about (by compromising your ISP? Sniffing non-TLS traffic?) then you may have a problem.”
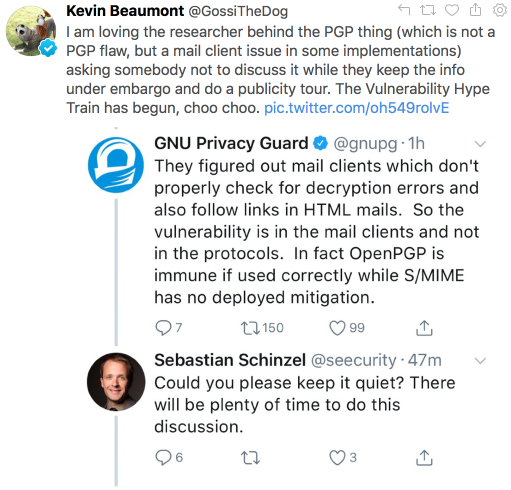
I can’t imagine anyone for whom email security is a critical issue would make all those mistakes, so this mostly merits a heads-up to the MUA developers (which has happened) and maybe a “Do people rely on S/MIME? Why?” retrospective. But as someone on twitter described it “The Vulnerability Hype Train has begin, choo choo.”
There are several different issues all mixed together by the efail folks. All of them require an attacker to already have access to (encrypted) sensitive emails, and to send copies of those to you wrapped up in another message and to have you decrypt that incoming mail.
- “Direct exfiltration”. Some mail clients with badly broken mime handling can apparently be convinced – if remote images are loaded automatically and email is decrypted automatically – to send decrypted plaintext to the attacker. This is bad, but mostly only applies to Apple Mail and Thunderbird. Apple have already fixed the issue on March 29th. And ErrataRob couldn’t replicate the claimed attack in current Thunderbird releases.
- “Indirect exfiltration of PGP encrypted messages”. It’s possible to inject plain text into an encrypted message in some cases. This isn’t particularly reliable. GPG and other OpenPGP implementations have mitigated this for many years, so it’ll only be possible to attack PGP if the implementation a mail client uses is faulty. That seems to be the case only for Thunderbird and Apple and a few niche clients. That can then be used to leak information about the decrypted text to the attackers server (via CSS, image loads, TLS OCSP requests, etc.).
- “Indirect exfiltration of S/MIME messages”. This is similar to the PGP approach but much more of an issue, both because S/MIME implementations seem to be far less robust against this sort of attack and because in the corporate environments where S/MIME is used it’s more likely to be installed by default with automatic decryption of messages (either on the desktop or on a corporate mail gateway). Attempts to exploit this will be really obvious, though, so in addition to MUAs fixing the issue (Apple have already fixed it, and I’d be surprised if Microsoft haven’t, though I pay less attention to their ecosystem) it’d be easy to block at the edge by pushing spam or malware filter updates.
The analysis on this seems good, technically. The cryptographic work appears solid – even if it’s pretty much just a rehash of decade old known issues. And the work done surveying clients for vulnerabilities is useful. MUA developers and people developing border mail filters should definitely read the paper.
But it follows the recent history of such disclosures, having a memorable name, it’s own website, a logo and announcement headlines chosen to get a response rather than top be accurate. This is primarily an issue with corporate encrypted email using S/MIME, but the announcements mostly describe it as being a bug in PGP (it isn’t) and stress it being used to attack those who use PGP – “journalists, political activists, whistleblowers, …” – which it probably isn’t, at least not successfully.

Keep your mail client updated. If privacy is important to you at all, don’t have it load remote content automatically.
And if you deal with sensitive emails that have to be encrypted and where someone may specifically be targeting you, you really have to try and understand what the threats against you are, as most of them aren’t as simple as this one. There’s no “do these five things and you’ll be secure” listicle.

 RSS - Posts
RSS - Posts