Zoho, phishing and who’s next?
ZDnet reports that Zoho’s problems with phishing aren’t over. Their report states that Zoho is being used as a pipeline to exfiltrate data from phished accounts.
The software platform’s email address service, on both zoho.com and zoho.eu domains, is being exploited in 40 percent of phishing campaigns in which email “is the primary exfiltration vehicle.”
That’s some serious problems.
Look, managing abuse and security is hard. Every online service is at risk and companies need to think not only about how they might be attacked but also how they may be a vector for attacks against others. Email is even more vulnerable than most services. Not only is email the key to online identity it’s also the vector for the majority of online attacks.
Companies running email services for customers must have two things.
- A security team that monitors infrastructure for attacks from bad actors. These attacks include “customers” attempting to identify vulnerabilities in your system so they can spam or phish through the system.
- A compliance team that monitors customers and acts on those “customers:” that managed to sneak through the automated defences.
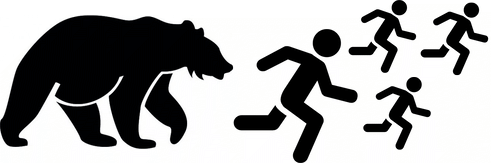
Every company that provides an email module in their platform is vulnerable. Every one. The big ESPs, the ISPs and the cable companies have pretty good defences these days. They’ve made spamming and phishing through their services hard enough that the bad guys are looking at much smaller companies.
No service is too small for them to look at. In fact, the smaller companies are ideal. Often the smaller companies outsource their infrastructure to a larger company, like SendGrid, Mandrill or Sparkpost. The spammers have been kicked directly off their platforms, but they can still spam through them, by abusing their customers.
The bad guys are getting smarter. They work hard to make themselves look like somewhat confused customers to extend any time on a platform. In every case they know they’re going to get cut off, at some point, they’re just trying to abuse the platform a little longer.
Compliance and security are hard. Being small is no excuse to ignore either.


