What SPF records should you publish?
When it comes to SPF records there seems to be a lot of confusion. I mean, a decade after I posted it Authenticating SPF is still the most frequently visited post on the site. And, of course, there are hundreds of other pages out there that discuss SPF and what to publish. Still, there are common questions.

Most recently I’ve been addressing questions about what SPF records need to be published. In the older post, I talk about how to publish, but don’t talk about what domains should be included. It’s probably time to do that.
What is SPF?
SPF is Sender Policy Framework. It allows domain owners to specify what IP addresses are expected to send mail from that domain.
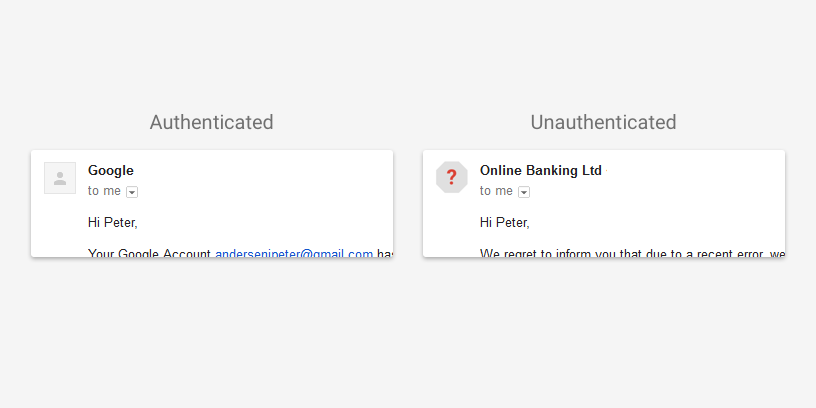
What does SPF authenticate?
Primarily, SPF authenticates the address in the Mail From:. This is not the domain that the final recipient sees in their mail client. The Mail From is also known as the envelope from, the bounce domain, the return path, the 5321.from, and other names..
The SPF spec also says that a lookup can be performed on the HELO value. During the SMTP transaction the first step is for the connecting server to introduce itself to the receiving server. These values can be things like “mx.wordtothewise.com” or “mail116-221.us32.msgfocus.com” It’s not a requirement to check this value, but it is an option.
What records should you publish?
SPF records should be published for the mail from address. I typically recommend publishing ~all. Back in 2009, I said there wasn’t much different in how ~all and -all were handled. This was true then, but recently I’ve become aware of a few large providers actively rejecting mail in cases where a -all is published and the sending IP is not in the SPF record.
It’s not uncommon for mail to be forwarded without altering the Mail From: causing SPF to become invalid. This is one of the reasons many ISPs didn’t reject based on SPF. With the advent of DMARC, it seems some ISPs are more confident in the accuracy of SPF records and thus are rejecting based on it. In light of these rejections, unless you really want mail rejected I still recommend using ~all.
What about the from address?
There are still a lot of ESPs and tutorials out there that suggest publishing SPF for the email address in the friendly from. Many years ago this was best practice because Microsoft would check SPF for the From address. It’s not going to hurt anything if you publish a SPF record for this domain, but it’s usually unnecessary.