Phishing and authentication
This morning I got a rather suspicious message from a colleague on LinkedIn.
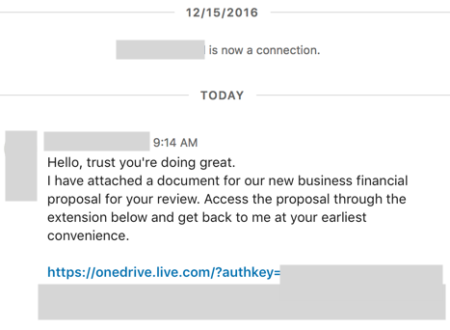
I asked around and it seems other folks got the same message and were equally confused. I didn’t click the link because that seemed risky. A few hours later one of the folks I had talked to mentioned that the person’s entire profile was gone. Likewise, the above message disappeared from my messages tab.
I’ll give LinkedIn credit. They acted quickly to remove the problematic content. I received the message at 9:30 this morning and by 1:30 the message and account were gone.
I often talk about how the email channel is very noisy and messy and ripe for abuse. But this incident shows that no channel is immune. And even authenticated channels can be subverted.
In the email space one attack vector is compromising individual user accounts and then using that account to send spam. Authentication is helpful, but as long as a third party can compromise an ESP account, we can’t rely solely on authentication to tell us what mail is good and what mail is bad.
In fact, there was a comment on mailop over the weekend where an individual said that spammers were much better at getting authentication right than legitimate mailers. And they authenticated at a much higher rate. I’m unsurprised, but glad to have someone actually say it.
It totally makes sense. Spammers deploy infrastructure for a few weeks or months, just long enough to get the spam out. They can automate the deployment with scripts – input the IP address, domains and the scripts create the website, DNS entries, set up the mail server and do all the things that need to be done.
Real companies don’t have it so simple. They’ve got to deal with legacy infrastructure, corporate policies, security, ESP functionality and a whole host of other things spammers don’t care about.