Crime
What about the botnets?!
Botnets are a huge problem for a number of reasons. Not only are they used to send spam, they’re also used in criminal activities. One of the major challenges in dealing with botnets is finding and stopping the people who create and use them. Why? Because the internet is global and crime tends to be prosecuted within local jurisdictions.
Security, safety and the cavalry
In some ways it’s been really hard to focus on email for the last few months. There are so many more important issues in the world. Terrorism, Brexit, the US elections compromised by a foreign government, nuclear threats from multiple countries, the repeal of ACA, mass deportations and ICE raids here in the US. I find myself thinking about what to blog. Then I glance at the news and wonder if there’s any value in another blog post about deliverability.
Generally I’ve tried to keep politics and world events mostly off the blog. But sometimes events are such that I need to talk about them.
Last October I had the chance to speak at the Email Innovations Summit in London. Steve and I took the chance to spend some time doing tourist things in London – including a photo walk along the Thames.
As an American I’m always a little surprised by the security in London. I grew up a few miles outside of DC. I could talk about prohibited airspace and security measures before I was 10. London is so much more open than even the DC of my youth. The surprise there is that London has been a much bigger target and attacked more than any city in the US.
The last few times we were in London I noticed a bit more visible security. In 2013 it was armed security walking through Tube stations. Last year it was Underground trains that were one long car. They were a bit weird and visually disconcerting. The part that really made me think, though, was this was a way to stop people hiding explosives between cars and to facilitate evacuations if something happened.
Last night Steve and I were talking and I mentioned the attack in London didn’t seem like terrorism to me. And it didn’t, not really. He then pointed out that explosives and guns are difficult to come by in the UK and this was classic terrorism. Oh. Sometimes our cultural differences come out in the strangest places.
Thinking about bigger issues like this make it hard to focus on email. There’s a regularly shared joke in deliverability, “There’s no such thing as a deliverability emergency.” And there isn’t, not really. Yes, even if a whole range of IPs is listed on Spamhaus, it’s still not an emergency and there’s no fast response team to deal with it.
There are abuse issues that are higher stakes than getting to the inbox. Child abuse materials. Harassment. Privacy issues. Terror threats. Every online services company, particularly the social media companies, have to deal with these kinds of things. Many of them are dealing poorly. Others have employees who are doing their best, but lack the tools, support, and training to do it well. Many companies don’t understand why they need to police their customer base.
The reality is, though, that abuse on the net (as opposed to abuse of the net) is a huge issue that needs to be dealt with. These are not small issues. The Internet is global and there’s no internet police. Law enforcement in different jurisdictions have to work together with technology experts to address crime and harassment on the internet.
It may surprise you to hear that the people who create spam filters and try and protect your inbox are the same people who fight crime on the internet. Spam and email are a vital part of online crime, so it falls on the abuse team to work with and educate law enforcement about tracing the source of email. The people you never see in ops, and abuse and support are vital to protecting folks online.
During the closing talk at MAAWG the chair was discussing how we can protect our online spaces. He stated “There is no cavalry; no second wave. It’s us or no one.” That’s a huge thing. My friends and colleagues are the people who stand protecting users online. It feels like a huge burden, but it’s something we can do to make the world a better and safer place.
Anatomy of a successful phishing attempt
Earlier this year the Exploratorium was the victim of a phishing attack. They’ve posted an article on what happened and how they discovered and dealt with the issue.
But they didn’t just report on the attack, they dissected it. And, as is appropriate for a organization with a mission of education, they mapped out what they discovered during the investigation.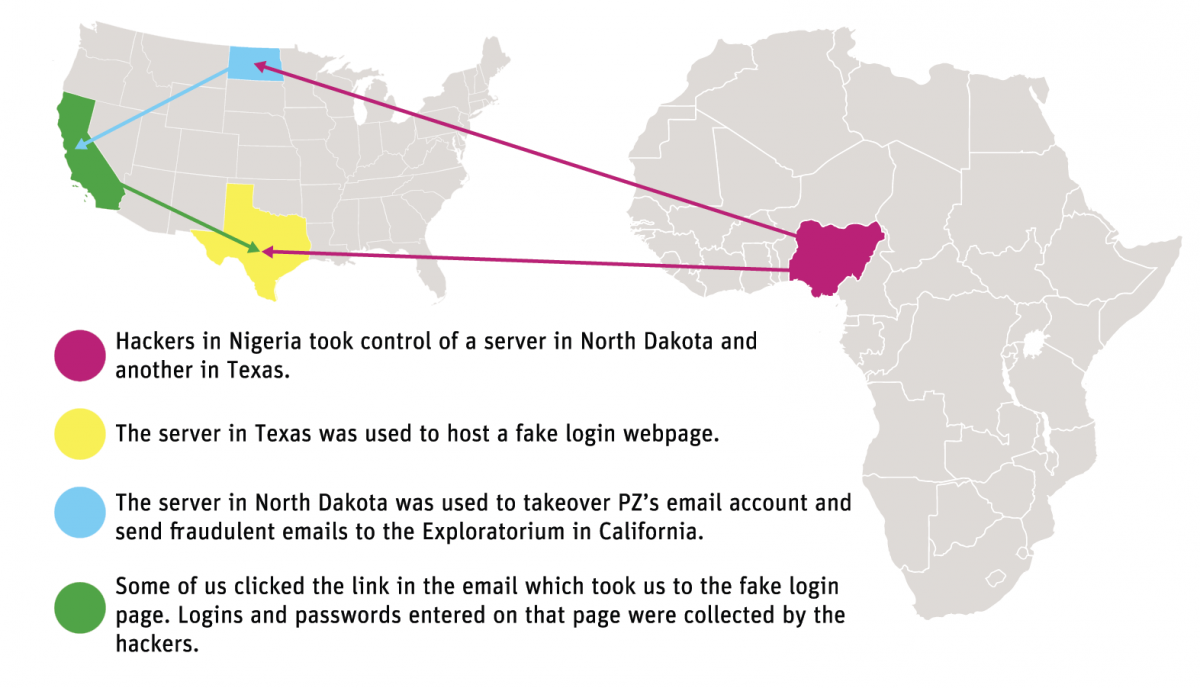
There are a couple of things that stand out to me about this attack. One is that of the more interesting pieces to me is that there was a delay between the compromise and the start of the attack. The Exploratorium calls it “the pivot” and describes it as the hacker deciding what to do next. The second is that the phisher actively interacted with the victim’s account. All new mail was sent to the trash automatically so she wouldn’t see incoming mail. Some mail was actively replied to so more people would click on the message. The phisher took steps to retain access to the account for as long as possible.
One thing that the Exploratorium didn’t see was any actual access to Exploratorium files or information. That may be because the Exploratorium itself wasn’t the target. Once a phisher / hacker has access to the email account, they have access to almost everything in your online life: calendars, bank accounts, credit accounts, the list goes on. Email addresses are our online identity and getting access to the address can open access to so much more.
Quite frankly it can happen to any of us. Earlier this week we received a phishing message that looked very plausible. It came from a law firm, mentioned a subpoena and even had an attachment personalized to our company. The attachment wasn’t opened so we were fine, but I can see how that kind of email might trick someone into getting infected.
We all need to be careful online. Email is a wonderful thing, but it’s insecure. It’s a great way for criminals to get into our space and wreck havoc on our computers and our lives.
Abuse, triage and data sharing
The recent subscription bombs have started me thinking about how online organizations handle abuse, or don’t as the case may be. Deciding what to address is all about severity. More severe incidents are handled first. Triage is critical, there’s never really enough time or resources to investigate abuse.
What makes an event severe? The answer is more complicated that one might think. Some of the things that ISP folks look at while triaging incoming complaints include:
Electronic records outside US not covered by US warrants
The 2nd Circuit Court of Appeals ruled against the Government today in US Government vs. Microsoft. The government is investigating a drug dealer and want access to records held by Microsoft. Microsoft turned over metadata stored on US machines. But they refused to turn over the specific emails stored on machines in Dublin. The company’s position is that the federal government needs to follow the rules of the Mutual Legal Assistance Treaty between the US and Ireland.
This has been winding its way through the appeals court.
The court’s ruling today states “§ 2703 of the Stored Communications Act does not authorize courts to issue and enforce against U.S.‐based service providers warrants for the seizure of customer e‐mail content that is stored exclusively on foreign servers.”
An interesting ruling, and I see pros and cons to the ruling. It does complicate anti-spam enforcement a bit and make it easier for criminals to hide their data overseas while they might be in the US. But it’s already easy for them to do that. Many arrests of spam gangs and others for crimes committed on the Internet over email involve multiple law enforcement agencies across the world.
Full text of the ruling (.pdf link)
Sanford Wallace goes to Jail
Sanford Wallace has been sentenced to 2 years in jail by the US District court in San Jose for contempt of court and electronic mail fraud. Sanford has been around for more than 2 decades. He is one of the spammers that drove me to learn how to read headers and report spam back in the late nineties.
Sanford has been in and out of courts and the news almost as long as he’s been spamming. When I dug into Pacer this morning to grab a copy of the sentencing report I see multiple cases, some going back as far as 1996. There aren’t electronic records for Concentric Network v. Wallace, et al. (case: 5:96-cv-20829-RMW) but the final disposition of the case says “Permanent Injunction.”
Phishing costs company $46 million
Brian Krebs posted about a tech firm that lost $46M dollars due to fraud. The company reported in its SEC filings that the money was lost when someone impersonated an employee and directed the finance department to transfer money to outside accounts.
This is becoming more common. In some cases, DMARC authentication may stop this kind of fraud. But DMARC has a lot of deployment challenges and can cause real mail to fail delivery. In other cases, criminals are using lookalike domains and they can be authenticated and pass DMARC.
This isn’t really a bulk mail issue. And it’s certainly not a deliverability issue. But it is a security issue and I think it’s important that folks are aware of this kind of online crime. Coincidentally, as I’m writing this, I’m chatting online with a compliance person at a cloud hosting company who is brainstorming policies to block phishing URLs on their site. Email is a major vector for abuse and those of us who manage sending need to be a part of the solution.
Filtering is not just about spam
A lot of filters started out just as filters against spam. But over the years they’ve morphed into more general blocks against dangerous or problematic email. There’s a lot of crime and bad behavior on the internet, much of it using email as a conduit or vector. Filtering is so much more than stopping spam now. It’s as much, or more, about stopping crime.
Email filters are essential to protect us from scammers. Sometimes I forget this, and then I read about a grandmother getting swindled by a Nigerian scammer and ending up dead.
There are real consequences to poor filtering and there is real crime facilitated by email. It’s easy to forget this as we deal with the email that gets caught in filters when they shouldn’t.
Filters are one of the first lines of defense against online crime.
Not only does filtering stop crime, but they also keep email working. An unfiltered mail stream is an ugly, unreadable, unworkable mess.
Email marketing firm smacked by the SEC
Yes, the SEC. Really.
Apparently the email marketing firm mUrgent, which provides services to the restaurant and hospitality industry also had a side business. According to the complaint filed by the SEC last month, they had an entire boiler room set up to sell shares for their non-existent IPO.
I’d never heard of this firm before, so I did a little digging. First step, check out their website.