Featured
What kind of mail do filters target?
All to often we think of filters as a linear scale. There’s blocking on one end, and there’s an inbox on the other. Every email falls somewhere on that line.![]() Makes sense, right? Bad mail is blocked, good mail goes to the inbox. The bulk folder exists for mail that’s not bad enough to block, but isn’t good enough to go to the inbox.
Makes sense, right? Bad mail is blocked, good mail goes to the inbox. The bulk folder exists for mail that’s not bad enough to block, but isn’t good enough to go to the inbox.
Once we get to that model, we can think of filters as just different tolerances for what is bad and good. Using the same model, we can see aggressive filters block more mail and send more mail to bulk, while letting less into the inbox. There are also permissive filters that block very little mail and send most mail to the inbox. That’s a somewhat useful model, but it doesn’t really capture the full complexity of filters. There isn’t just good mail and bad mail. Mail isn’t simply solicited or unsolicited. Filters take into account any number of factors before deciding what to do with mail.
That’s a somewhat useful model, but it doesn’t really capture the full complexity of filters. There isn’t just good mail and bad mail. Mail isn’t simply solicited or unsolicited. Filters take into account any number of factors before deciding what to do with mail.
October 2017: The Month in Email
October was a busy month. In addition to on boarding multiple new clients, we got new desks, I went to Toronto to see M3AAWG colleagues for a few days, and had oral surgery. Happily, we’re finally getting closer to having the full office setup. 
What is an office without a Grover Cat? (he was so pleased he figured out how to get onto it at standing height).
All of this means that blogging was pretty light this month.
One of the most interesting bits of news this month is that the US National Cybersecurity Assessments & Technical Services Team issued a mandate on web and email security, which Steve reviewed here.
In best practices, I made a brief mention about the importance of using subdomains rather than entirely new domain names in links and emails and even DKIM keys.
We’ve talked about engagement-based filters before, but it’s interesting to note how they’re being used in business environments as well as consumer environments.
We also put together a survey looking at how people use Google Postmaster Tools. The survey is now closed, and I’ll be doing a full analysis over the next couple of weeks, as well as talking about next steps. I did a quick preview of some of the highlights earlier this week.
Finally, a lot of industry news this month: Most notably, Mailchimp has changed its default signup process from double opt-in to single opt-in. This caused quite a bit of sturm und drang from all ends of the industry. And, in fact, a few days later they announced the default double-opt-in would stay in place for .eu senders. I didn’t get a chance to blog about that as it happened. In other news, the Road Runner FBL is permanently shuttered, and Edison Software has acquired Return Path’s Consumer Insight division. Also worth noting: Microsoft is rolling out new mail servers, and you’ll likely see some new — and potentially confusing — error codes.
My October themed photo is behind a cut, for those of you who have problems with spiders.
September 2017: The Month in Email
Happy October! ‘Tis the season for “the scariest costumes to wear to an inbound marketing Halloween party”. Terrifying, right? A perfect occasion for spam-infused mai tais!
In other news from the blog in September, I wrote several posts about the Equifax breach, starting with the announcement of the compromise on September 7th and their utterly inadequate response, followed by more incompetence when they sent people to the wrong site to get assistance. I also noted some of the discussion around the various educational paths people working in information security have and why these are the wrong questions to ask.
Speaking of the various paths people take towards careers in email, I wrote a followup post on Shiva Ayyadurai, whose defamation suit around his claims to being the inventor of email was recently dismissed.
I wrote a few posts about Gmail, including a guide to improving Gmail delivery, and some specific advice on how to warm up your Gmail mailstream, which is somewhat different than other warmup processes. In other news on mail providers, it’s worth noting some recent changes Microsoft has made to various domains.
In best practices, Steve wrote about a nice series of emails we received following an online purchase and I wrote about properly monitoring your DMARC reports.
Every now and then, I like to return to the basics. My post on 10 Things Every Mailer Must Do is a handy overview to share with your team (or your customers, if you’re an ESP). If you’re having delivery challenges and haven’t tackled these top ten best practices, this is where you need to start. I wrote up some additional thoughts on how we think about deliverability that you might find useful as well.
August 2017: The month in email
Hello! Hope all are keeping safe through Harvey, Irma, Katia and the aftermath. I know many people that have been affected and are currently out of their homes. I am proud to see so many of my fellow deliverability folks are helping our displaced colleagues with resources, places to stay and money to replace damaged property.
Here’s a mid-month late wrapup of our August blog posts. Our favorite part of August? The total eclipse, which was absolutely amazing. Let me show you some pictures.



Ok, back to email.
We’re proud of the enormous milestone we marked this month: ten years of near-daily posts to our Word to the Wise blog. Thanks for all of your attention and feedback over the past decade!
In other industry news, I pointed to some interesting findings from the Litmus report on the State of Email Deliverability, which is always a terrific resource.
I also wrote about the evolution of filters at web-based email providers, and noted that Gmail’s different approach may well be because it entered the market later than other providers.
In spam, spoofing, and other abuse-related news, I posted about how easy it is for someone to spoof a sender’s identity, even without any technical hacks. This recent incident with several members of the US presidential administration should remind us all to be more careful with making sure we pay attention to where messages come from. How else can you tell that someone might not be wholly legitimate and above-board? I talked about some of what I look at when I get a call from a prospective customer as well as some of the delightful conversations I’ve had with spammers over the years.
In the security arena, Steve noted the ongoing shift to TLS and Google’s announcement that they will label text and email form fields on pages without TLS as “NOT SECURE”. What is TLS, you ask? Steve answers all your questions in a comprehensive post about Transport Layer Security and Certificate Authority Authorization records.
Also worth reading, and not just for the picture of Paddington Bear: Steve’s extremely detailed post about local-part semantics, the chunk of information before the at sign in an email address. How do you choose your email addresses (assuming they are not assigned to you at work or school…)? An email address is an identity, both culturally and for security purposes.
In subscription best practices — or the lack thereof — Steve talked about what happens when someone doesn’t quite complete a user registration. Should you send them a reminder to finish their registration? Of course! Should you keep sending those reminders for 16 months after they’ve stopped engaging with you? THE SURPRISING ANSWER! (Ok, you know us. It wasn’t that surprising.)
July 2017: The month in email
August is here, and as usual, we’re discussing spam, permissions, bots, filters, delivery challenges, and best practices.
One of the things we see over and over again, both with marketers and with companies that send us email, is that permission is rarely binary — companies want a fair amount of wiggle room, or “implied permission” to send. There are plenty of examples of how companies try to dance around clear permissions, such as this opt form from a company we used to do business with. But there are lots of questions here: can you legitimately mail to addresses you haven’t interacted with in 5 years? 10 years? What’s the best way to re-engage, if at all?
We frequently get questions about how to address deliverability challenges, and I wrote up a post about some of the steps we take as we help our clients with this. These are short-term fixes; for long-term success, the most effective strategy is sending email that people want and expect. Engagement is always at the core of a sustainable email program.
We’ve also discussed the rise of B2B spam, and the ways in which marketing technologies contribute to the problem. B2B marketers struggle to use social and email channels appropriately to reach customers and prospects, but still need to be thoughtful about how they do it. I also wrote about some of the ways that marketing automation plugins facilitate spam and how companies should step up to address the problem. Here’s an example of what happens when the automation plugins go awry.
I wrote a few posts about domain management and the implications for security and fraud. The first was about how cousin domain names can set users up for phishing and fraud, and the second was a useful checklist for looking at your company’s domain management. We also looked at abuse across online communities, which is an increasing problem and one we’re very committed to fighting.
I also highlighted a few best practices this month: guidelines for choosing a new ESP and active buttons in the subject line for Gmail.
And finally, we celebrated the 80th birthday of the original SPAM. If you’re a regular reader of this blog, you probably already know why unwanted email is called SPAM, but just in case, here’s a refresher….
April 2017: The Month in Email
April was a big travel month for us. I went to Las Vegas for meetings around the Email Innovations Summit and to New Orleans, where Steve spoke on the closing keynote panel for the EEC conference.
I wrote several posts this month about privacy and tracking, both in email and in other online contexts. It’s increasingly a fact of life that our behaviors are tracked, and I wrote about the need for transparency between companies and those they are tracking. More specifically, I talked about the tradeoffs between convenience and security, and how people may not be aware that they are making these tradeoffs when they use popular mailbox tools like unroll.me. The folks over at ReturnPath added a comment on that post about how they handle privacy issues with their mailbox tools.
Steve contributed several posts this month. First up, a due diligence story about how service providers might look more closely at potential customers for their messaging platforms to help curtail spam and other fraudulent activity. He also looked at the history of “/8” IP blocks, and what is happening to them as the internet moves to IPv6. Steve also added a note about his new DMARC Validation tool, which rounds out a suite of free tools we’ve made available on our site. And finally, he showcased a particularly great email subscription experience from Tor.com — have a look!
I highlighted another post about companies doing things right, this one by Len Shneyder over at Marketingland. In other best practices news, I talked about bounce handling again (I mentioned it last month too), and how complicated it can be. Other things that are complicated: responding to abuse complaints. Do you respond? Why or why not?
Our friends at Sendgrid wrote a great post on defining what spammers and other malicious actors do via email, which I think is a must-read for email marketers looking to steer clear of such activity. Speaking of malicious actors, I wrote two posts on the arrest of one of the world’s top email criminals, Peter Levashov, and speculation that he was involved in the Russian hacking activity around the US elections. We’re looking forward to learning more about that story as it unfolds.
March 2017: The Month in Email
It’s that time again… here’s a look at our last month of blog posts. We find it useful to recap each month, both to track trends and issues in email delivery and to provide a handy summary for those who aren’t following along breathlessly every single day. Let us know if you find it useful too!
As always, I wrote about email filters. It’s so important to recognize that filters aren’t arbitrary — they’re detailed instructions that help meet specific user needs, and the more you are cognizant of that, the better you’ll be able to work with them. Additionally, filters aren’t perfect and likely never will be. False positives and false negatives are frustrating, but as long as spam is still a viable business for spammers, they’ll continue to figure out how to work around filters. As such, we can’t expect filters to be 100% accurate in determining what constitutes wanted and unwanted mail.
Part of this, of course, is due to the problem of fraudulent signups. Companies aren’t particularly vigilant about address acquisition and hygiene, and as a result, they’ll claim you “signed up” for their email when you did not. Some people believe that a confirmed opt-in (COI) will solve this problem, but our experience is companies are reluctant to leave revenue on the table, and that they will continue to mail to addresses that have not confirmed.
Address sharing and co-reg is also part of the problem. As we saw in the extensive RCM data breach, many major brands continue to work with third-party senders to send mail in ways that are quite clearly spam. And in more criminal activity, I looked at the rise of botnets and how some of those criminals were brought to justice. In other justice news, there’s been an indictment in the Yahoo breach and another CASL enforcement action.
I wrote a post about bounce handling and “relaying denied” error messages, which are quite rare. It’s useful to have an understanding of these and other error messages, since bounces are sometimes indicative of a larger technical issue, such as when AOL accidentally bounced all messages for a short period last week. Speaking of AOL, we noted that there’s no official timeline for the move from Verizon addresses to AOL addresses following the 2015 acquisition, but it may be worth considering asking your customers to update their addresses.
Spam and filters aren’t the only factors of course. It can be challenging to figure out the multiple factors that make up the black box of delivery. And of course, the most important part of delivery continues to be engagement, engagement, engagement.
I wrote a few posts this month on why I do what I do, and why it’s so important to me. First, I wrote about A Day Without A Woman, and my choice not to participate in offering advice and guidance for that day. The truth is that I enjoy sharing what I know and helping people solve problems. I was honored to be named one of 11 Innovators in Email, and I know that my volunteer work in the industry and my unpaid blogging work is a big part of that. It may sound corny, but I really do believe we are on the front lines of the fight of good vs. evil online, and despite the distractions of politics and world events, we must all continue to do our part.
September 2016: The month in email
Happy October, everyone. As we prepare to head to London for the Email Innovations Summit, we’re taking a look back at our busy September. As always, we welcome your feedback, questions, and amusing anecdotes. Seriously, we could use some amusing anecdotes. Or cat pictures.

We continued to discuss the ongoing abuse and the larger issues raised by attacks across the larger internet infrastructure. It’s important to note that even when these attacks aren’t specifically targeting email senders, security issues affect all of us. It’s important for email marketers to understand that increased attacks do affect how customers view the email channel, and senders must take extra care to avoid the appearance of spam, phishing, or other fraudulent activity. I summarized some of the subscription form abuse issues that we’re seeing across the web, and noted responses from Spamhaus and others involved in fighting this abuse. We’re working closely with ESPs and policy groups to continue to document, analyze and strategize best practices to provide industry-wide responses to these attacks.
I was pleased to note that Google is stepping up with a new program, Project Shield, to help journalists and others who are being targeted by these attacks by providing hosting and DDoS protections.
I’m also delighted to see some significant improvements in email client interactions and user experiences. I wrote a bit about some of those here, and I added my thoughts to Al’s discussion of a new user interaction around unsubscribing in the iOS 10 mail client, and I’ll be curious to see how this plays out across other mail clients.
For our best practices coverage, Steve wrote about global suppression lists, and the ways these are used properly and improperly to prevent mail to certain addresses. I wrote about using the proper pathways and workflows to report abuse and get help with problems. I also wrote about the ways in which incentivizing address collection leads to fraud. This is something we really need to take seriously — the problem is more significant than some bad addresses cluttering up your lists. It contributes to the larger landscape of fraud and abuse online, and we need to figure out better ways to build sustainable email programs.
Is there such a thing as a perfect email? I revisited a post from 2011 and noted, as always, that a perfect email is less about technology and more about making sure that the communication is wanted and expected by the recipient. I know I sound like a broken record on this point (or whatever the 21st century equivalent metaphor of a broken record is….) but it’s something that bears repeating as marketers continue to evolve email programs.
We had a bit of a discussion about how senders try to negotiate anti-spam policies with their ESPs. Is this something you’ve experienced, either as a sender or an ESP?
In Ask Laura, I covered shared IP addresses and tagged email addresses, questions I get fairly frequently from marketers as they enhance their lists and manage their email infrastructures. As always, we welcome your questions on all things email delivery related.
April 2016: The Month in Email
We are finishing up another busy month at WttW. April was a little nutty with network glitches, server crashes, cat woes, and other disruptions, but hopefully that’s all behind us as we head into May. I’ll be very busy in May as well, speaking at Salesforce Connections in Atlanta and the Email Innovation Summit in Las Vegas. Please come say hello if you’re attending either of these great events.
Speaking of great events, I participated in two panels at EEC16 last month. We had a lot of great audience participation, and I met many wonderful colleagues. I wrote up some more thoughts about the conference here. I also had a nice conversation with the folks over at Podbox, and they’ve posted my interview on their site.
In the Podbox interview, as always, I talked about sending mail people want to receive. It always makes me roll my eyes a bit when I see articles with titles like “5 Simple Ways to Reach the Inbox”, so I wrote a bit about that here. In addition to sending mail people want to receive, senders need to make sure they are collecting addresses and building lists in thoughtful and sustainable ways. For more on this topic, check out my post on list brokers and purchased lists.
These same not-so-simple tricks came up again in my discussion of Gmail filters. Everyone wants a magic formula to reach the inbox, and — sorry to burst your bubble — there isn’t ever going to be one. And this is for a good reason: a healthy filter ecosystem helps protect all of us from malicious senders and criminal activity. The email channel is particularly vulnerable to fraud and theft. The constant evolution of filters is one way mail providers can help protect both senders and recipients — but it can be challenging for senders and systems administrators to keep up with this constant evolution. For example, companies sometimes even inadvertently filter their own mail!
I also wrote a bit about how B2B spam is different from B2C spam, and how marketers can better comply with CAN SPAM guidelines in order to reach the inbox. We also republished our much-missed friend and colleague J.D. Falk’s DKIM Primer, which is extremely useful information that was at a no-longer-active link.
One of my favorite posts this month was about “dueling data”, and how to interpret seemingly different findings around email engagement. We also got some good questions for my “Ask Laura” column, where we cover general topics on email delivery. This month we looked at “no auth/no entry” and the Microsoft Smartscreen filter, both of which are useful things to understand for optimizing delivery.
Finally, we are pleased to announce that we’ve joined the i2Coalition, an organization of internet infrastructure providers. They posted a nice introduction on their blog, and we look forward to working with them to help advocate and protect these important technical infrastructures.
February 2016: The Month in Email
Happy March! Here’s a look back at our last month of email adventures. It was a busy few weeks for us with the M3AAWG meeting in San Francisco. We saw lots of old friends and met many new people — all in all, a success, despite the M3AAWG plague we both contracted. Hot topics at the conference included DMARC, of course, and I took the opportunity to write up a guide to help you determine if you should publish a DMARC policy.
It was a busy few weeks for us with the M3AAWG meeting in San Francisco. We saw lots of old friends and met many new people — all in all, a success, despite the M3AAWG plague we both contracted. Hot topics at the conference included DMARC, of course, and I took the opportunity to write up a guide to help you determine if you should publish a DMARC policy.
On the subject of advice and guidance, Ask Laura continues to be a popular column — we’ve had lots of interesting questions, and are always looking for more general questions about email delivery. We can’t tackle specifics about your program in this column (get in touch if we can help you with that directly) but we can help with questions like “Will our ESP kick us off for mailing purchasers?” or “Help! I’m confused about authentication.”
Continuing on the authentication front, I noted that Gmail is starting to roll out some UI to indicate authentication status to users. It will be interesting to see if that starts to affect user (or sender) behavior in any way. In other interesting industry news, Microsoft has implemented an Office 365 IP Delisting page. I also wrote a followup post to my 2015 overview of the state of ESPs and purchased lists — it’s worth checking out if this is something your business considers.
I wrote a post about security and backdoors, prompted by both the FBI/Apple controversy and by Kim Zetter’s talk at M3AAWG about Stuxnet. These questions about control and access will only get more complicated as we produce, consume, store, and share more data across more devices.
Speaking of predictions, I also noted my contribution to a great whitepaper from Litmus that explores the state of Email Marketing in 2020.
As always, we looked at some best practices this month. I wrote up some of my thoughts about data hygiene following Mailchimp’s blog post about the value of inactive subscribers. As always, there isn’t one right answer, but there’s a lot of good food for thought. And more food for thought: how best practices are a lot like public health recommendations. As with everything, it comes down to knowing your audience(s) and looking at the relationship(s), which, as you know, is a favorite subject around here.
Yes, Virginia, there is list churn
Yesterday I talked about how data collection, management, and maintenance play a crucial role in deliverability. I mentioned, briefly, the idea that bad data can accumulate on a list that isn’t well managed. Today I’d like to dig into that a little more and talk about the non-permanence of email addresses.
A common statistic used to describe list churn is that 30% of addresses become invalid in a year. This was research done by Return Path back in the early 2000’s. The actual research report is hard to find, but I found a couple articles and press releases discussing the info.
June 2015: the Month in Email
Happy July! We are back from another wonderful M3AAWG conference and enjoyed seeing many of you in Dublin. It’s always so great for us to connect with our friends, colleagues, and readers in person. I took a few notes on Michel van Eeten’s keynote on botnets, and congratulated our friend Rodney Joffe on winning the prestigious Mary Litynski Award.
In anti-spam news, June brought announcements of three ISP-initiated CAN-SPAM cases, as well as a significant fine leveled by the Canadian Radio-television and Telecommunications Commission (CRTC) against Porter Airlines. In other legal news, a UK case against Spamhaus has been settled, which continues the precedent we’ve observed that documenting a company’s practice of sending unsolicited email does not constitute libel.
In industry news, AOL started using Sender Score Certification, and Yahoo announced (and then implemented) a change to how they handle their Complaint Feedback Loop (CFL). Anyone have anything to report on how that’s working? We also noted that Google has discontinued the Google Apps for ISPs program, so we expect we might see some migration challenges along the way. I wrote a bit about some trends I’m seeing in how email programs are starting to use filtering technologies for email organization as well as fighting spam.
Steve, Josh and I all contributed some “best practices” posts this month on both technical issues and program management issues. Steve reminded us that what might seem like a universal celebration might not be a happy time for everyone, and marketers should consider more thoughtful strategies to respect that. I wrote a bit about privacy protection (and pointed to Al Iverson’s post on the topic), and Josh wrote about when senders should include a physical address, what PTR (or Reverse DNS) records are and how to use them, testing your opt-out process (do it regularly!), and advice on how to use images when many recipients view email with images blocked.
Deliverability and IP addresses
Almost 2 years ago I wrote a blog post titled The Death of IP Based Reputation. These days I’m even more sure that IP based reputation is well and truly dead for legitimate senders.
There are a lot of reasons for this continued change. 
April 2015: The Month in Email
We started the month with some conversations about best practices, both generally looking at the sort of best practices people follow (or don’t) as well as some specific practices we wanted to look at in more depth. Three for this month:
Read MoreA series of tubes
The Internet and pundits had a field day with Senator Stevens, when he explained the Internet was a series of tubes.
I always interpreted his statement as coming from someone who demanded an engineer tell him why his mail was delayed. The engineer used the “tube” metaphor to explain network congestion and packets and TCP, and when the Senator tried to forward on the information he got it a little wrong. I do credit the Senator with trying to understand how the Internet works, even if he got it somewhat wrong. This knowledge, or lack there of, drove his policy positions on the issue of Net Neutrality.
In the coming years, I believe we’re going to be seeing more regulations around the net, both for individuals and for corporations. These regulations can make things better, or they can make things worse. I believe it’s extremely important that our elected officials have a working understanding of the Internet in order to make sensible policy. This understanding doesn’t have to be in their own head, they can hire smart people to answer their questions and explain the implications of policy.
Apparently I’m not the only one who thinks it is important for our elected officials to have a working knowledge of technology. Paul Schreiber put up a blog post comparing the website technology used by the current Presidential candidates. Do I really expect the candidate to be involved in decisions like what domain registrar or SSL certificate provider to use? No. But I do expect them to hire people who can create and build technology that is within current best practices.
March 2015: The month in email
Happy March! We started the month with some more movement around CASL enforcement from our spam-fighting friends to the north. We noted a $1.1 million fine levied against Compu-Finder for CASL violations, as well as a $48,000 fine to Plentyoffish Media for failing to provide unsubscribe links. We noted a few interesting things: the fines are not being imposed at the maximum limits, violations are not just on B2C marketing, but also on B2B senders, and finally, that it really just makes sense — both from a delivery perspective and a financial perspective — to comply with the very reasonable best practices outlined in CASL.
Read MoreFebruary 2015 – The month in email
This was a short and busy month at WttW!
We attended another great M3AAWG conference, and had our usual share of interesting discussions, networking, and cocktails. I recapped our adventures here, and shared a photo of the people who keep your email safe while wearing kilts as well. We also commended Jayne Hitchcock on winning the Mary Litynski award for her work fighting abuse and cyberstalking.
Read MoreEmail predictions for 2015
Welcome to a whole new year. It seems the changing of the year brings out people predicting what they think will happen in the coming year. It’s something I’ve indulged in a couple times over my years of blogging, but email is a generally stable technology and it’s kind of boring to predict a new interface or a minor tweak to filters. Of course, many bloggers will go way out on a limb and predict the death of email, but I think that’s been way over done.
Even major technical advancements, like authentication protocols and the rise of IPv6, are not usually sudden. They’re discussed and refined through the IETF process. While some of these changes may seem “all of a sudden” to some end users, they’re usually the result of years of work from dedicated volunteers. The internet really doesn’t do flag days.
One major change in 2014, that had significant implications for email as a whole, was a free mail provider abruptly publishing a DMARC p=reject policy. This caused a lot of issues for some small business senders and for many individual users. Mailing list maintainers are still dealing with some of the fallout, and there are ongoing discussions about how best to mitigate the problems DMARC causes non-commercial email.
Still, DMARC as a protocol has been in development for a few years. A number of large brands and commercial organizations were publishing p=reject policies. The big mail providers were implementing DMARC checking, and rejection, on their inbound mail. In fact, this rollout is one of the reasons that the publishing of p=reject was a problem. With the flip of a switch, mail that was once deliverable became undeliverable.
Looking back through any of the 2014 predictions, I don’t think anyone predicted that two major mailbox providers would implement p=reject policies, causing widespread delivery failures across the Internet. I certainly wouldn’t have predicted it, all of my discussions with people about DMARC centered around business using DMARC to protect their brand. No one mentioned ISPs using it to force their customers away from 3rd party services and discussion lists.
I think the only constant in the world of email is change, and most of the time that change isn’t that massive or sudden, 2014 and the DMARC upheaval notwithstanding.
But, still, I have some thoughts on what might happen in the coming year. Mostly more of the same as we’ve seen over the last few years. But there are a couple areas I think we’ll see some progress made.
Changing the email client
We’re in the thick of hiring and next week is Thanksgiving, so blogging is going to be very light for the next two weeks.
One thing I have noticed is that lately there are attempts to “change how people interact with email.” Google released their Inbox product. And today I saw a post about an IBM attempt to change email and how people use it as a tool.
I find as I juggle more and more incoming email that most email clients just don’t cope with the whole process well. For a long time I could use my inbox as a todo list and manage what needed to be done. With the company growing and changing, an inbox todo list is just not as workable as it used to be. Maybe the Verse client from IBM is one solution.
I’m glad people are looking at how to improve the email client. Fundamentally, the client I’m using now is not that much different than the GUI client I was using at MAPS back in 2000 and 2001. Sure, it’s visually different, but the functionality isn’t much different.
A few years ago I blogged that people should look at building new email interfaces. I’m glad that some companies are actually looking at the interface and rethinking how people interact with email. Who knows, maybe we’ll end up with some specialized clients that are featured around getting work done by email and other clients focused around a more casual use of email, like shopping and networking.
October 2014 – The Month in Email
October was action-packed at WttW. We wrapped up some big and interesting client projects (look for some case studies soon!), attended another great M³AAWG conference, and made an exciting announcement that we’re hiring a deliverability specialist. The combination of these frees up some more of my time for blogging, which I’ve really missed. Look for more from me in November and December.
Read MoreSeptember 2014: The Month in Email
September was another busy month for us, but Steve stepped up and wrote a number of really interesting posts on email history, cryptography, and current technical issues in the email landscape.
We started the month with a look at the various RFCs that served as the technical specifications for developing message transfer protocols in the 1970s. It’s really fascinating to look at the evolution of these tools we use every day 40 years later. We followed up with a second post on the origins of network email, which is a great primer (or refresher) on the early days of email.
Steve’s four-part series on cryptography and email started with an in-depth look at how the industry is evolving with respect to encryption and privacy issues. He then introduced us to Alice and Bob (or reintroduced those of us who have been following the adventures of the first couple of cryptography), and described symmetric-key and public-key encryption. His next post described message signing, and how DKIM is used to manage this. He finished up the series with a post on PGP keys.
In industry news: Spamcop is shutting down its email service. There shouldn’t be any major impact on senders, but the post has some specific notes on DMARC implications. We also noted an interesting mail routing suggestion on Twitter, and wrote a post on using Mail.app for this.
In other DMARC news, we wrote about DMARC and report size limits, which might be useful information, depending on your configuration. We also launched a new DMARC tool to help senders understand who is publishing DMARC. Let us know what you think and if you’re finding it useful.
We couldn’t let a month go by without mentioning filters. We looked at a sector we don’t usually discuss, corporate filtering, and went in-depth on a much-misunderstood topic, content filtering.
Finally, Laura offered a webinar on a favorite topic, deliverability, in conjunction with the AMA and Message Systems. If you missed it, you can watch the recorded version here, or just take a peek at some of the reaction via Twitter.
Think you know about deliverability?
Check out the tweets from my AMA webinar sponsored by Message Systems today.
Thanks to the AMA and Message Systems for having me.
Email History through RFCs
Many aspects of email are a lot older than you may think.
There were quite a few people in the early 1970s working out how to provide useful services using ARPANET, the network that evolved over the next 10 or 15 years into the modern Internet.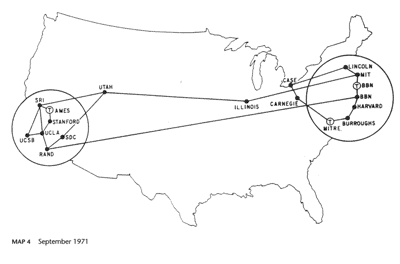
They used Requests for Comment (RFCs) to document protocol and research, much as is still done today. Here are some of the interesting milestones.
April 1971 [rfc 114]RFC 114 A File Transfer Protocol.[/rfc] One of the earliest services that was deployed so as to be useful to people, rather than a required part of the network infrastructure, was a way to transfer files from one computer to another. In the [rfc 114]earliest versions[/rfc] of the service I can find it could already append text to an existing file. This was soon used for sending short messages, initially to a remote printer from where it would be sent by internal mail, but soon also to a mailbox where they could be read online.
August 1971 [rfc 221]RFC 221 A Mail Box Protocol, Version-2[/rfc] had this prescient paragraph:
Unsubscribing is hard
A comment came through on my post about unsubscribing that helpfully told me that the problem was I didn’t unsubscribe correctly.
As you know, there are usually two unsubscribe options in many of the bulk senders emails. Are you unsubscribing from the global or the offer unsub? Unless you are unsubscribing from both, you will still be on the lists.
To address the underlying question, I did unsubscribe from both links for those very few mails in my mailbox that had double unsubscribe links. I know that some spammers use multiple unsubscribe links in their emails. We routinely recommend clients not use 3rd party mailers with double unsubscribes because it’s a clear sign the 3rd party mailer is a spammer.
Given the presence of double unsubscribes I generally assume the point is to confuse recipients. By having multiple unsubscribe links the spammers can ignore unsubscribe requests with the excuse that “you unsubscribed from the wrong link.” Plausible deniability at its finest. The best part for the spammer is that it doesn’t matter which unsubscribe link the recipient picks, it will always be the Wrong One.
I’ve been dealing with spam since the late 90s, and have been professionally consulting on delivery for over 14 years. If I can’t figure out what link to use to unsubscribe, how is anyone supposed to figure out how to make mail stop?
In some cases, the unsubscribe links admitted that the address I was trying to unsubscribe was already removed from the list. They helpfully refused to let me unsubscribe again through their form. But they offered a second way to unsubscribe.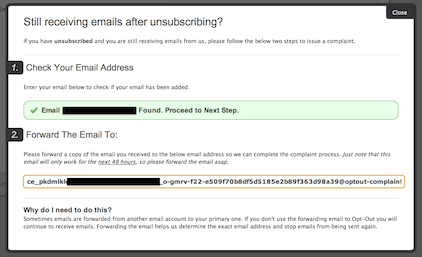
The address I was unsubscribing was the same one I was unsubscribing. Some of the emails even helpfully told me “this email was sent to trapaddress@” which is the address in the above screenshot.
I’m sure my friend will come back and comment with “why didn’t you unsubscribe by forwarding the email?” Because I was spending enough time unsubscribing as it was, and I didn’t want to have to try and navigate yet another unsubscribe process. I knew they weren’t going to stop mailing me, no matter what hoops I jumped through.
I’m not saying that all unsubscribe processes are broken, there are millions and millions of emails sent every day with simple and effective unsubscribe links. What I am saying is that there is a lot of mail getting to inboxes that users never requested nor wanted. “Just unsubscribing” from this mail Does Not Work. It just keeps coming and coming and coming.
But of course, the mail still coming is my fault, as I was unable to correctly unsubscribe. 
July 2014: The month in email
We continue to be busy with really interesting client work. Look for some new posts and white papers to come out of this research over the next few months, but for now blogging has been a bit light while we’re working hard. In parallel with our busy times, we have also been pondering the ways in which the email world illustrates the classic bon mot “plus ça change, plus c’est la même chose”, and we’ve been revisiting some posts from a few years ago to examine this.
We started July with a nod to a good subscription experience just as CASL, the Canadian Anti-Spam Legislation went into effect on Canada Day. While companies have another 17 months to put these provisions into practice, it’s a good reminder that periodic re-engagement with customers can be very effective in helping you maintain high-quality subscriber lists. We talked a bit more about CASL here and what protections the law intends.
In stark contrast, we posted about an organization that is doing a less-than-stellar job making sure they’re only sending wanted email. The Direct Marketing Association is a terrific resource and member organization for marketers across industries and channels, but their email marketing practices don’t always live up to their mission of “Advancing and Protecting Responsible Data-Driven Marketing”, and we explored some ways in which they might improve this.
Those of you who have been reading this blog for any time at all know that we tend to talk about wanted mail and unwanted mail rather than the more general category of spam. Marketers tend to think their mail can’t possibly be spam if it’s not offering Viagra or phishing for credit card information, but that’s not really the point — if a customer doesn’t want to read your email about new mountain bikes, even if they bought a mountain bike from you three years ago, that’s unwanted email. Here’s a post we revisited about why customers might not want your mail, and a new post about engagement.
One risk of sending unwanted email, of course, is that customers complain, and that will affect your delivery going forward. We revisited a post about feedback loops, and also talked a bit about addressing delivery problems as they come up rather than waiting for them to resolve on their own (mostly, they won’t!)
I also proposed a bit of a thought experiment around monetizing the complaint stream, and followed up with a second post. There are some good points in the comments of those posts, but mostly I think it’s an interesting solution to addressing risk and abuse at ESPs.
Finally, Steve wrote a short post about our new mail servers and how quickly spammers descended as we set those up. It’s a constant battle!
CASL is more privacy law than anti-spam law
Michael Geist, a law professor in Canada, writes about the new CASL law, why it’s necessary and why it’s more about privacy and consumer protection than just about spam.
Read MoreJune 2014: The month in email
Each month, we like to focus on a core email feature or function and present an overview for people looking to learn more. This month, we addressed authentication with SPF.
We also talked about feedback mechanisms, and the importance for senders to participate in FBL processes.
In our ongoing discussions about spam filters, we took a look at the state of our own inboxes and lamented the challenge spam we get from Spamarrest. We also pointed out a post from Cloudmark where they reiterate much of what we’ve been saying about filters: there’s no secret sauce, just a continuing series of efforts to make sure recipients get only the mail they want and expect to receive. We also looked at a grey area in the realm of wanted and expected mail: role accounts (such as “marketing@companyname.com”) and how ESPs handle them.
As always, getting into the Gmail inbox is a big priority for our clients and other senders. We talked a bit about this here, and a bit more about the ever-changing world of filters here.
On the subject of list management, we wrote about the state of affiliate mailers and the heightened delivery challenges they face getting in the inbox. We got our usual quota of spam, and a call from a marketer who had purchased our names on a list. You can imagine how effective that was for them.
And in a not-at-all-surprising development, spammers have started to employ DMARC workarounds. We highlighted some of the Yahoo-specific issues in a post that raises more questions.
We also saw some things we quite liked in June. In the Best Practices Hall of Fame, we gave props to this privacy policy change notification and to our bank’s ATM receipts.
We also reviewed some interesting new and updated technology in the commercial MTA space, and were happy to share those findings.
Ever changing filtering
One of the ongoing challenges sending email, and managing a high volume outbound mail server is dealing with the ongoing changes in filtering. Filters are not static, nor can they be. As ISPs and filtering companies identify new ways to separate out wanted email from unwanted email, spammers find new ways to make their mail look more like wanted mail.
This is one reason traps are useful to filtering companies. With traps there is no discussion about whether or not the mail was requested. No one with any connection to the email address opted in to receive mail. The mail was never requested. While it is possible for trap addresses to get on any list monitoring mail to spam traps is a way to monitor which senders don’t have good practices.
New filtering techniques are always evolving. I mentioned yesterday that Gmail was making filtering changes, and that this was causing a lot of delivery issues for senders. The other major challenge for Gmail is the personalized delivery they are doing. It’s harder and harder for senders to monitor their inbox delivery because almost every inbox is different at Gmail. I’ve seen different delivery in some of my own mailboxes at Gmail.
All of this makes email delivery an ongoing challenge.
Role accounts, ESPs and commercial email
There was a discussion today on a marketing list about role accounts and marketing lists. Some ESPs block mail to role accounts, and the discussion was about why and if this is a good practice. In order to answer that question, we really need to understand role accounts a little more.
Read MoreUpdates to commercial MTAs
Last week Message Systems announced the release of Momentum 4. This high volume MTA has a large number of features that make it possible for large volume senders to manage their email and their delivery. I had the opportunity to get a preview of the new features and was quite impressed with the expanded features. Improvements that caught my eye include:
Read MoreSpam filters and mailbox usage
It’s no secret that I run very little in the way of spam filters, and what filters I do run don’t throw away mail, they just shove it into various mailboxes.
Looking at my mailboxes currently I have 11216 unread messages in my mail.app junk folder, 10600 unread messages in my work spam assassin folder and 29401 messages in my personal spam assassin folder (mail getting more than +7 on our version of spam assassin gets filtered into these folders). I went through and marked all of my messages read back in mid-January. That’s a little over 50,000 messages in a little over 5 months or slightly more than 2700 spams a week.
But these are messages I don’t have to deal with so while they’re somewhat annoying and a bit of “wow, my addresses are everywhere” they’re not a huge deal. I have strong enough filters for wanted mail that I can special case it.
May 2014: The month in email
It’s been a busy and exciting month for us here.
Laura finished a multi-year project with M3AAWG, the Messaging, Malware and Mobile Anti-Abuse Working Group (look for the results to be published later this year) and continued working with clients on interesting delivery challenges and program opportunities. Steve focused on development on the next version release of Abacus, our flagship abuse desk tool, which will also be available later this year.
And as always, we had things to say about email.
The World of Spam and Email Best Practices
We started the month with a bit of a meta-discussion on senders’ fears of being labeled spammers, and reiterated what we always say: sending mail that some people don’t want doesn’t make you evil, but it is an opportunity to revisit your email programs and see if there are opportunities to better align your goals with the needs of people on your email lists. We outlined how we’ve seen people come around to this position after hitting spamtraps. That said, sometimes it is just evil. And it’s still much the same evil it’s been for over a decade.
We also wrote a post about reputation, which is something we get asked about quite frequently. We have more resources on the topic over at the WiseWords section of our site.
Gmail, Gmail, Gmail
Our friends over at Litmus estimate Gmail market share at 12%, which seems pretty consistent with the percentage of blog posts we devote to the topic, yes? We had a discussion of Campaign Monitor’s great Gmail interview, and offered some thoughts on why we continue to encourage clients to focus on engagement and relevance in developing their email programs. We also wrote a post about how Gmail uses filters, which is important for senders to understand as they create campaigns.
SMTP and TLS
Steve wrote extensively this month about the technical aspects of delivery and message security. This “cheat sheet” on SMTP rejections is extremely useful for troubleshooting – bookmark it for the next time you’re scratching your head trying to figure out what went wrong.
He also wrote a detailed explanation of how TLS encryption works with SMTP to protect email in transit, and followed that with additional information on message security throughout the life of the message. This is a great set of posts to explore if you’re thinking about security and want to understand potential vulnerabilities.
DKIM
Steve also wrote a series of posts about working with DKIM (DomainKeys Identified Mail), the specification for signing messages to identify and claim responsibility for messages. He started with a detailed explanation of DKIM Replay Attacks, which happens when valid email is forwarded or otherwise compromised by spammers, phishers or attackers. Though the DKIM signature persists (by design) through a forward, the DKIM specification restricts an attacker’s ability to modify the message itself. Steve’s post describes how senders can optimize their systems to further restrict these attacks. Another way that attackers attempt to get around DKIM restrictions is by injecting additional headers into the message, which can hijack a legitimately signed message. If you’re concerned about these sort of attacks (and we believe you should be), it’s worth learning more about DKIM Key Rotation to help manage this. (Also of note: we have some free DKIM management tools available in the WiseTools section of our site.)
As always, we’re eager to hear from you if there are topics you’d like us to cover in June.
The more things change
I was doing some research about the evolution of the this-is-spam button for a blog article. In the middle of it, I found an old NY Times report about spam from 2003.
Read MoreIP reputation and email delivery
IP reputation is a measure of how much wanted mail a particular IP address sends. This wanted mail is measured as a portion of the total email sent from that IP. Initially IP reputation was really the be all and end all of reputation, there was no real good way to authenticate a domain or a from address. Many ISPs built complex IP reputation models to evaluate mail based on the IP that sent the mail.
These IP reputation models were the best we had, but there were a lot of ways for spammers to game the system. Some spammers would create lots of accounts at ISPs and use them to open and interact with mail. Other spammers would trickle their mail out over hundreds or thousands of IPs in the hopes of diluting the badness enough to get to the inbox. Through it all they kept trying to get mail out through reputable ESPs, either by posing as legitimate customers or compromising servers.
These things worked for a while, but the ISPs started looking harder at the recipient pool in order to figure out if the interactions were real or not. They started looking at the total amount of identical mail coming from multiple IP addresses. The ISPs couldn’t rely on IP reputation so they started to dig down and get into content based filtering.
As the ISPs got better at identifying content and filtering on factors other than source IP, the importance of the IP address on inbox delivery changed. No longer was it good enough to have a high reputation IP sending mail.
These days your IP reputation dictates how fast you can send mail to a particular ISP. But a high reputation IP isn’t sufficient to get all the mail in the inbox. It’s really content that drives the inbox / bulk folder decisions these days.
Generally IPs that the ISP has not seen email traffic from before start out with a slight negative reputation. This is because most new IPs are actually infected machines. The negative reputation translates to rate limiting. The rate limiting minimizes people getting spam while the ISP works out if this is a real sender or a spammer.
Some ISPs put mail in the inbox and bulk foldering during the whitelisting process. In this case what they’re doing is seeing if your recipients care enough about your mail to look for it in the bulk folder. If they do, and they mark the mail as “not spam” then this feeds back to the sender reputation and the IP reputation.
If you’re seeing a lot of bulk foldering of mail, it’s unlikely there’s anything IP reputation based to do. Instead of worrying about IP reputation, focus instead on the content of the mail and see what you may need to do to improve the reputation of the domains and URLs (or landing pages) in the emails.
April: The month in email
April was a big month of changes in the email world, and here at Word to the Wise as we launched our new site, blog and logo.
DMARC
The big story this month has been DMARC, which started with a policy change Yahoo made on April 4 updating their DMARC policy from “report” to “reject”. We began our coverage with a brief DMARC primer to explain the basics around these policy statements and why senders are moving in this direction. We shared some example bounces due to Yahoo’s p=reject, and talked about how to fix discussion lists to work with the new Yahoo policy. We gathered some pointers to other articles worth reading on the Yahoo DMARC situation, and suggested some options for dealing with DMARC for mail intermediaries. Yahoo issued a statement about this on April 11th, explaining that it had been highly effective in reducing spoofed email. We also noted a great writeup on the situation from Christine at ReturnPath. On April 22nd, AOL also announced a DMARC p=reject record. We talked a bit about who might be next (Gmail?) and discussed how Comcast chose to implement DMARC policies, using p=reject not for user email, but only for the domains they use to communicate directly with customers. We expect to see more discussion and policy changes over the next few weeks, so stay tuned.
Spamtraps
We wrote three posts in our continuing discussion about spamtraps. The first was in response to a webinar from the DMA and EEC, where we talked about how different kinds of traps are used in different ways, and, again, how spamtraps are just a symptom of a larger problem. Following that, we wrote more about some ongoing debate on traps as we continued to point out that each trap represents a lost opportunity for marketers to connect with customers, which is really where we hope email program managers will focus. And finally, we tried to put some myths about typo traps to rest. As I mentioned in that last post, I feel like I’m repeating myself over and over again, but I want to make sure that people get good information about how these tools are used and misused.
Security
We started the month by saying “Security has to become a bigger priority for companies” and indeed, the internet continued to see security breaches in April, including the very serious Heartbleed vulnerability in SSL. In the email world, AOL experienced a compromise, which contributed to some of the DMARC policy changes we discussed above. In a followup post, we talked about how these breaches appear to be escalating. Again, we expect to hear more about this in the next weeks and months.
Best Practices
Ending on a positive note, we had a few posts about best practices and some email basics. We started with a pointer to Al Iverson’s post on masking whois info and why not to do it. Steve wrote up a comprehensive post with everything you ever wanted to know about the From header and RFC5322. I talked about how companies ignore opt-outs, and why they shouldn’t. I shared a really good example of a third-party email message, and also talked about message volume. And finally, we talked about how and why we warm up IP addresses.
Let us know if there’s anything you’d like to hear more about in May!
Welcome to our new site
We’re very excited and pleased to launch our redesigned website and blog.
As you can see, we have a new logo and an official color scheme. In addition to the cosmetic changes, we’ve improved the underlying structure. We have pages dedicted to our offerings, including Abacus and information about our consulting services.
We’ve also consolidated a lot of the information spread across different website. The ISP Information page is updated and current (finally! all the Goodmail references are gone). And the ISP specific pages are here instead of over on the wiki.
Two features we’re quite excited about are our wiseWords and wiseTools.
wiseWords is our place to publish more in depth articles about email, delivery and the Internet than the blog. Over time, I expect this to grow to encompas a full email knowledge base. We’ve also published some white papers for download.
wiseTools is the umbrella for our useful email tools, including the tools published at emailstuff.org. They’re still at emailstuff.org, but they’re also here at tools.wordtothewise.com.
We’ve done our best to make sure links transfer from the old site to the new one, but feel free to contact us if you find a broken link.
You may find your first comment on the new blog goes into moderation the first time you post. But once you’ve been approved, comments won’t go through moderation a second time.
Our new website is just the first of many new things we are hoping to roll out in the coming months.